![[Easy for Non-Majors] Information Security Incidents: From Cause Analysis by Type to SolutionsCourse Thumbnail](https://cdn.inflearn.com/public/files/courses/342007/cover/ai/2/785d01a5-f55f-4807-b882-6dcbfe3d7f91.png?w=420)
[Easy for Non-Majors] Information Security Incidents: From Cause Analysis by Type to Solutions
88888
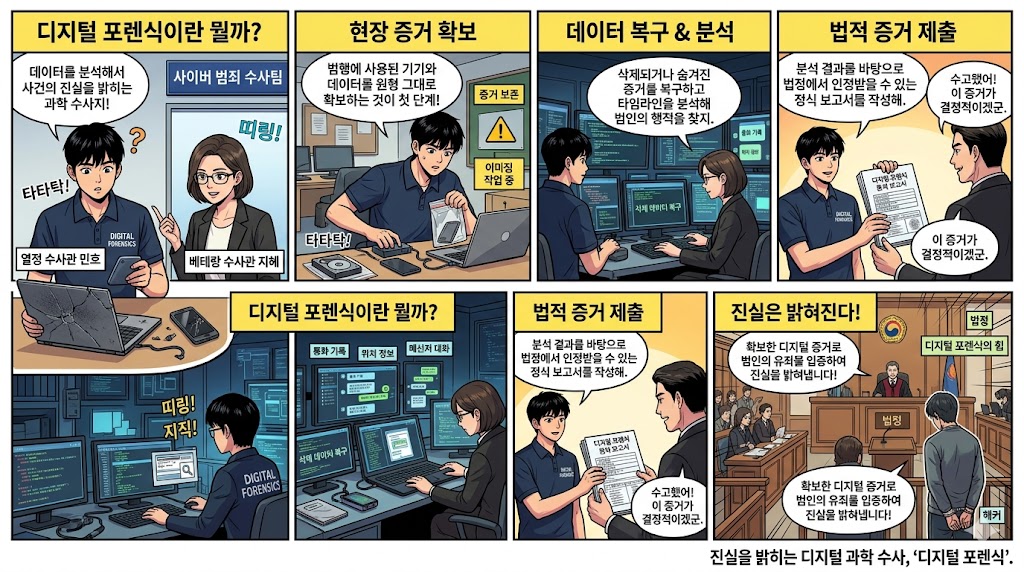
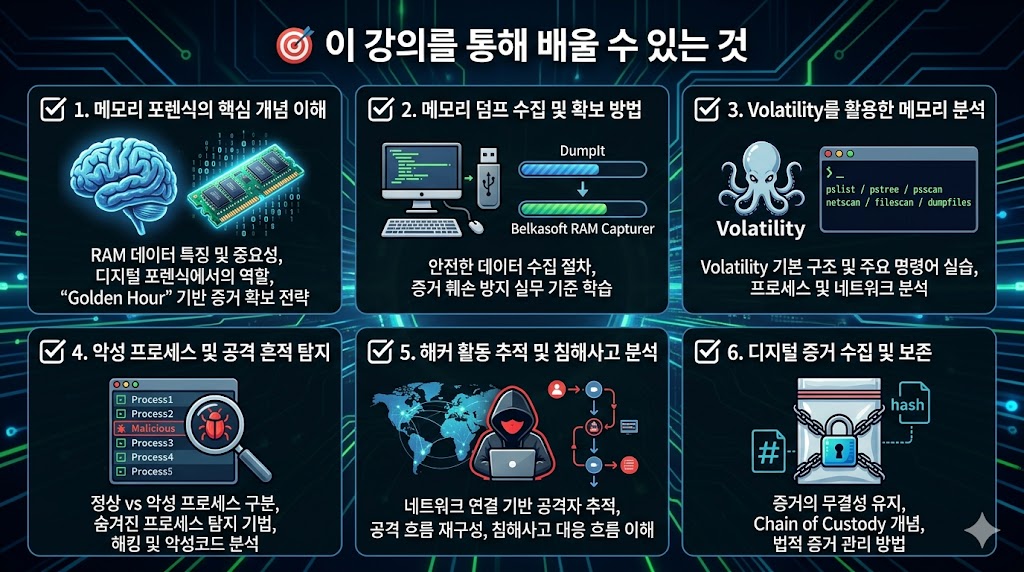
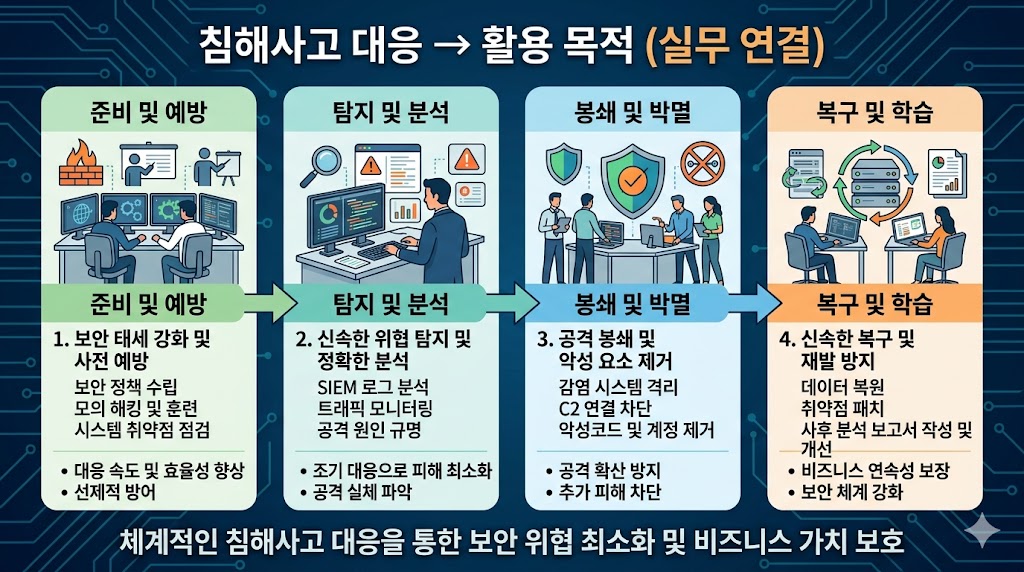
[Introduction to Security Incident Response: Learning through Scenarios of Web Server Hacking, Ransomware, and Account Takeover] This course examines why various information security incidents—such as web server hacking, ransomware, account takeover, and internal penetration—occur and how they spread, categorized by incident type. Students will follow each incident scenario to understand the attack flow, analyze the core causes of the incident, and learn how to resolve issues and prevent recurrence through security architectures such as firewalls, DMZ, access control, privilege management, backup, and log monitoring. Rather than a simple explanation of security concepts, this is a scenario-based introduction to information security that provides a comprehensive understanding from root cause analysis to resolution strategies.
Beginner
Penetration Testing, Network, Computer Architecture











![[D-PEC UP_PASS] National Certified Intellectual Property Ability Test (IPAT) Preparation (Core Compression)Course Thumbnail](https://cdn.inflearn.com/public/files/courses/338414/cover/ai/2/7df16b1f-6503-44f6-90c2-3a4b00802b72.png?w=420)


![[Deep-Up_ONE] Understanding Corporate IT Systems in One GoCourse Thumbnail](https://cdn.inflearn.com/public/files/courses/341417/cover/ai/2/bfab075d-63e3-4b79-a37b-000e4e1d1549.png?w=420)

![[D-PEC UP_PASS] Nationally Certified Industrial Security Expert (ISE)Course Thumbnail](https://cdn.inflearn.com/public/files/courses/333129/cover/ai/0/67228f11-355f-4e72-86c5-4c7d1b906a63.png?w=420)