System Hacking & Reversing: Learning Everything from Beginner to Intermediate in One Go
knockOn
A complete curriculum for those learning hacking for the first time. From beginner to intermediate, finish it all with a single course.
Basic
System Hacking, security training






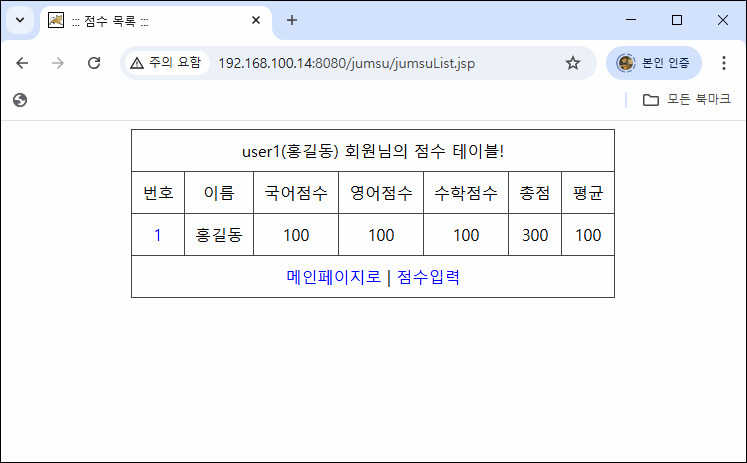


![Introduction to Linux and Linux Kernel Overview [Author's Lecture Part 1-1]Course Thumbnail](https://cdn.inflearn.com/public/courses/333097/cover/8e09c5df-0571-462e-878c-39ddf13549b6/333097.png?w=420)




![Structure and Principles of the Linux Kernel: Interrupt Bottom Halves [Author's Lecture Part 1-6]Course Thumbnail](https://cdn.inflearn.com/public/courses/333195/cover/3b8c8cd2-44b0-43b7-a441-b950ba367717/333195.png?w=420)




