
웹 개발자와 정보보안 입문자가 꼭 알아야 할 웹 해킹 & 시큐어 코딩
크리핵티브
정보보안 입문자와 웹 개발자 분들을 위한 웹 해킹 입문 강의! 본 강의를 시작으로 웹 해킹을 재미있게 시작해보세요!
초급
모의해킹, 인젝션
The second lecture on SQL Injection, taught by a mock hacking practitioner! The first lecture covered the basics and the core principles of attacks, while the second lecture is about technical advanced attack techniques. Therefore, taking the first lecture is a must!
SQL Injection application attack technique
Advanced SQL Injection Attack Techniques
New Blind-Based SQL Injection
Advanced/Applied SQL Injection Attack Techniques You've Never Seen Before!
We present a new direction for mock hacking attacks.
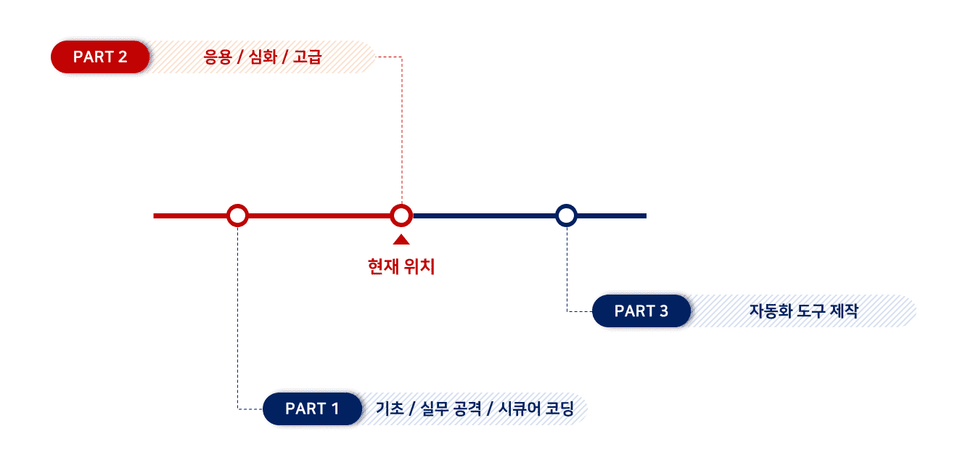

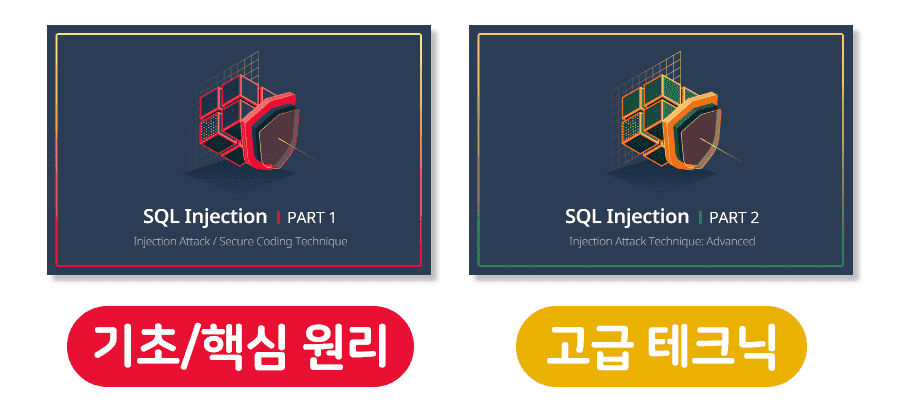
If the previous lecture Part (1) was about the basics and principles of attacks, and the core theory and practice of attacks, this lecture covers the technical aspects of SQL Injection attacks . Therefore, Part (1) is the backbone of this lecture, so it is recommended that you take Part (1) first and then Part (2).
If any of the items below apply to you, you can solve them quickly and easily through this lecture!
This lecture covers not only known attack techniques, but also techniques that we discovered through our own research rather than well-known attack techniques. This attack technique presents a new direction for Blind-Based SQL Injection attacks !
The lecture also covers how this attack technique can be used to query data faster and more effectively than previously known attack techniques!
So... practitioners must definitely take this course, right!?
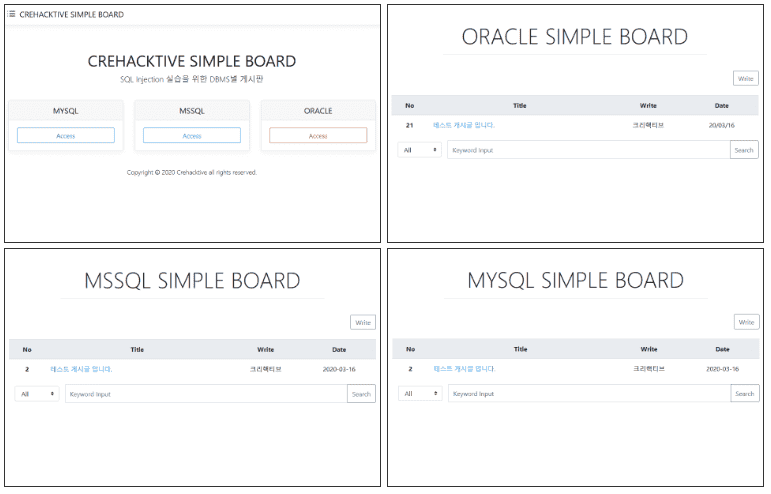
We provide a practice bulletin board based on PHP-MYSQL, PHP-MSSQL, and PHP-ORACLE, through which you can practice SQL Injection for various DBMS.
Q. Can I understand Part (2) lecture if I haven't taken Part (1) lecture?
A. I highly recommend that you take the Part (1) lecture. I also recommend that you take this lecture after you have a sufficient understanding of SQL Injection attacks. If you have not taken Part (1) but have sufficient knowledge of SQL Injection attacks, there will be no major problems in taking Part (2), but there may be terms used or content that you are not familiar with, so I recommend that you take Part (1) if possible.
Q. Is this an attack technique that can be applied directly in practice?
A. Yes, of course! It can be applied immediately and attacks can be made more efficiently than existing technologies.
Q. Is there any information about countermeasures?
A. No, there isn't. For the countermeasures, please refer to the Part (1) lecture.
※ Nanum font provided by Naver is used in this training PPT.
Who is this course right for?
Someone who has basic knowledge of SQL Injection
Anyone who is confident about SQL Injection attacks
For those who want to know more about SQL Injection attacks
Anyone who wants to make SQL Injection attacks faster
Need to know before starting?
SQL Basic Grammar
SQL Injection Basic Knowledge
Understanding SQL Injection Attacks
26,165
Learners
1,387
Reviews
502
Answers
4.9
Rating
18
Courses
안녕하세요, 크리핵티브입니다.
다년간 다양한 웹 서비스를 진단하고 연구한 경험을 바탕으로, 실무에 바로 적용 가능한 지식을 인프런 플랫폼에서 공유해오고 있습니다.
그리고 웹 해킹 기초를 체계적으로 다룬 『크리핵티브의 한 권으로 끝내는 웹 해킹 바이블』을 집필했습니다. 기초가 부족한 분들께는 이 책으로 학습을 시작하실 것을 권합니다.
『크리핵티브의 한 권으로 끝내는 웹 해킹 바이블』 저자
이메일 : crehacktive3@naver.com
All
85 lectures ∙ (14hr 43min)
Course Materials:
All
24 reviews
4.9
24 reviews
Reviews 4
∙
Average Rating 5.0
Reviews 1
∙
Average Rating 5.0
Reviews 17
∙
Average Rating 4.8
Reviews 4
∙
Average Rating 5.0
Reviews 1
∙
Average Rating 3.0
$127.60
Check out other courses by the instructor!
Explore other courses in the same field!