How to use Notion perfectly
boanproject
Learn how to use Notion, the next hottest app after Evernote, step-by-step from the beginning with a focus on practice.
Beginner
Business Productivity, Notion, Project Management (PM)
Network packet analysis is essential when conducting incident analysis and vulnerability analysis. Among the tools available, Wireshark is the most widely used, and this course covers the complete utilization of Wireshark and provides understanding through incident analysis case studies.
7,848 learners
Level Basic
Course period Unlimited

Reviews from Early Learners
5.0
DM
It's a good lecture.
5.0
이장희
Thank you for the informative lecture^^
5.0
jeong033
It is well explained so that beginners can easily approach it. It was very helpful~
Incident Response Packet Analysis Cases
How to Use Wireshark
Network Packet Analysis
The goal of this course is to equip students with the ability to conduct in-depth analysis of network packets generated in actual security incidents and simulated hacking scenarios. Upon completion of the training, you will acquire the following capabilities.
You will clearly understand the network-level operating principles of various security threats (web hacking, system vulnerabilities, database attacks, etc.).
You can identify and analyze the characteristics of packets generated by major security tools such as Nessus, Metasploit, Nikto, and others.
We will build the foundation of network forensics and incident response analysis by linking security event logs and network traffic that occur in real-world scenarios to reconstruct the full story of incidents.
Case-based practical lectures 💻 Rather than stopping at theoretical explanations, we intensively analyze packet samples based on actual security incident analysis cases and simulated hacking scenarios. You'll directly see with your own eyes 'what attacks leave what packets' to maximize your practical sense.
Various Hacking Tool Packet Analysis 🛠️ We cover in-depth attack packets using web vulnerability assessment tools (Arachni, Nikto, WPScan), system vulnerability analysis tools (Nessus), and the flagship attack framework (Metasploit). Through this, we cultivate essential attack traffic analysis skills for both defenders and penetration testing professionals.
Attack Scenario-Based Learning ⚔️ Beyond simple packet analysis, we track packets based on clear attack scenarios such as FTP anonymous access attacks, MySQL database hacking attempts, and system remote control. Through this, you develop the ability to understand the entire flow of an attack from start to finish.
- Security project management and representative
- Security consulting and training for over 200 large and small companies
- (Former) KB Securities IT Planning Information Security Team
- (Former) A3Security penetration testing team
- (Former) Multicampus IT security external expert instructor
- (Former) Chung-Ang University Industrial Security Department visiting professor
- (Former) Seoul Digital University visiting professor
Published Books
- Android Mobile App Penetration Testing (Acorn Publishing, 2017)
- Complete Web Penetration Testing Practice Using bWAPP (Hanbit Media, 2016)
- IT Engineer Side Job, Publishing Books (Bfanbooks, 2015)
- Burp Suite Utilization and Web Penetration Testing (Hanbit Media, 2015)
- WordPress Plugin Vulnerability Analysis and Penetration Testing (Hanbit Media, 2015)
- How to Live as an IT Engineer 1 (Bfanbooks, 2015)
- Android Mobile Malware and Penetration Testing Diagnosis (Acorn Publishing, 2014)
- What is Penetration Testing (Wikibooks, 2014)
- Penetration Testing Using Kali Linux (Acorn Publishing, 2014)
- The World of Digital Forensics (Infothebooks, 2014)
- Master Detective Hacker Who Catches Crackers (Seongan Publishing, 2010)
Published over 30 books including
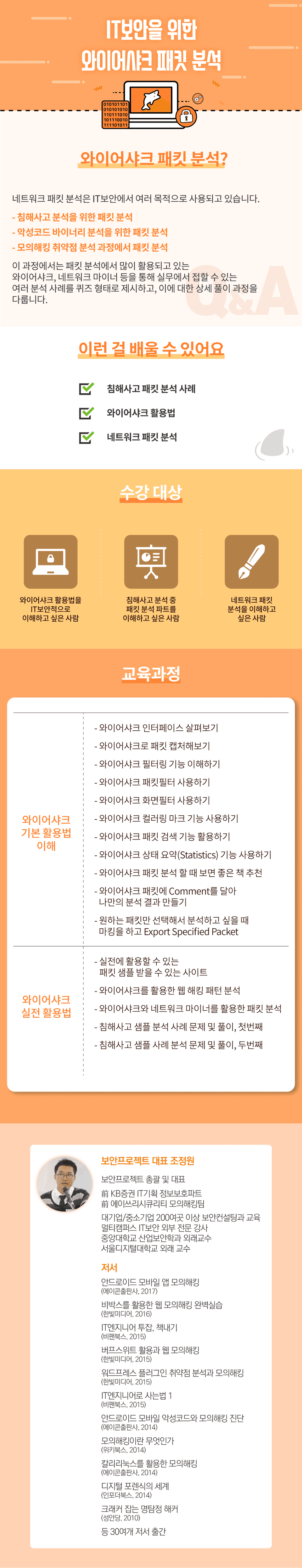
Who is this course right for?
Someone who wants to understand how to use Wireshark from an IT security perspective
Someone who wants to understand the packet analysis part during incident response analysis
People who want to understand network packet analysis
Need to know before starting?
Understanding Basic Protocols
Understanding Networks
103,863
Learners
3,316
Reviews
445
Answers
4.7
Rating
67
Courses
Boan Project ( www.boanproject.com ) provides online and group lectures in various fields, including IT security, big data, machine learning, and IoT.
All
33 lectures ∙ (6hr 34min)
Course Materials:
All
210 reviews
4.8
210 reviews
Reviews 4
∙
Average Rating 5.0
Reviews 4
∙
Average Rating 5.0
Reviews 1
∙
Average Rating 5.0
Reviews 2
∙
Average Rating 5.0
Reviews 29
∙
Average Rating 5.0
Check out other courses by the instructor!
Explore other courses in the same field!