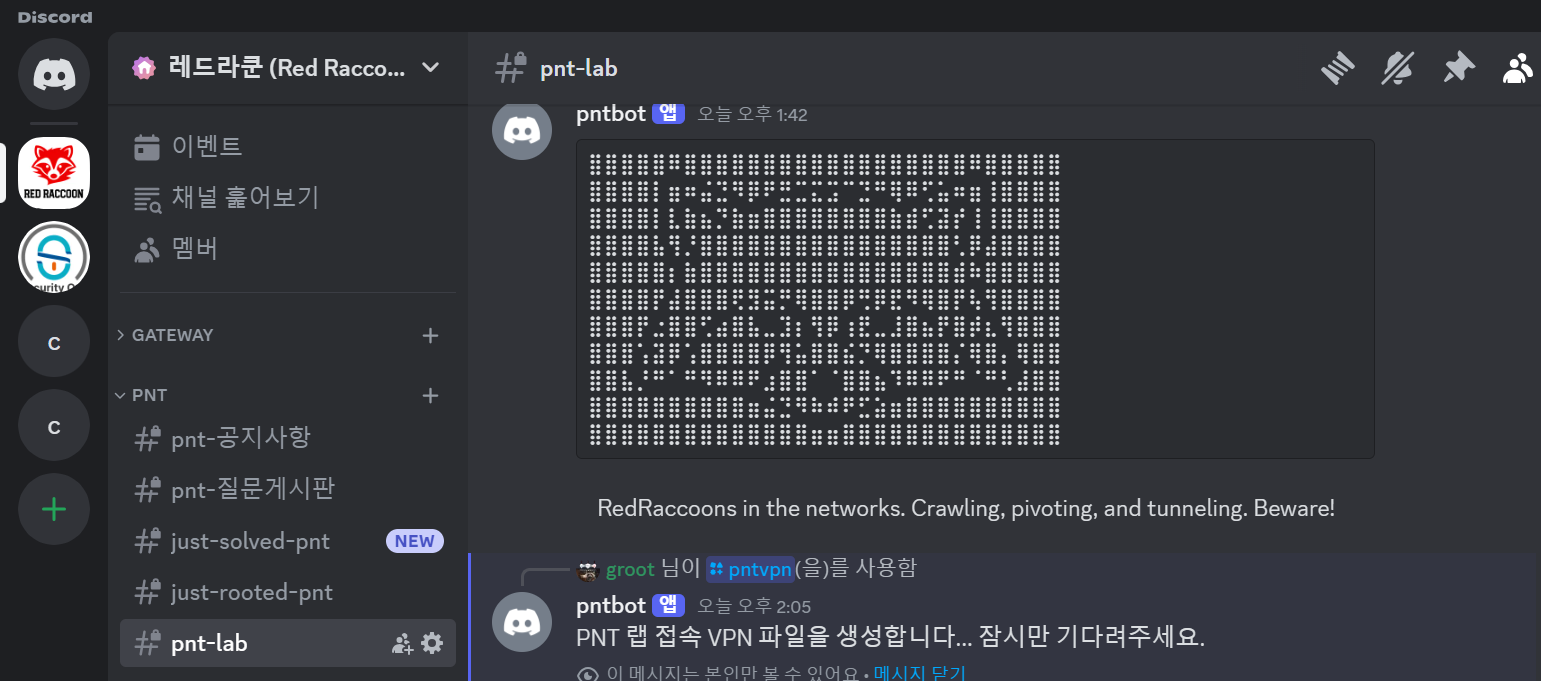
Red Raccoon Community
Red Raccoon is a cybersecurity community that not only provides lectures on cybersecurity hacking techniques but also shares cybersecurity topics, tips, and know-how.
➡Red Raccoon Website List
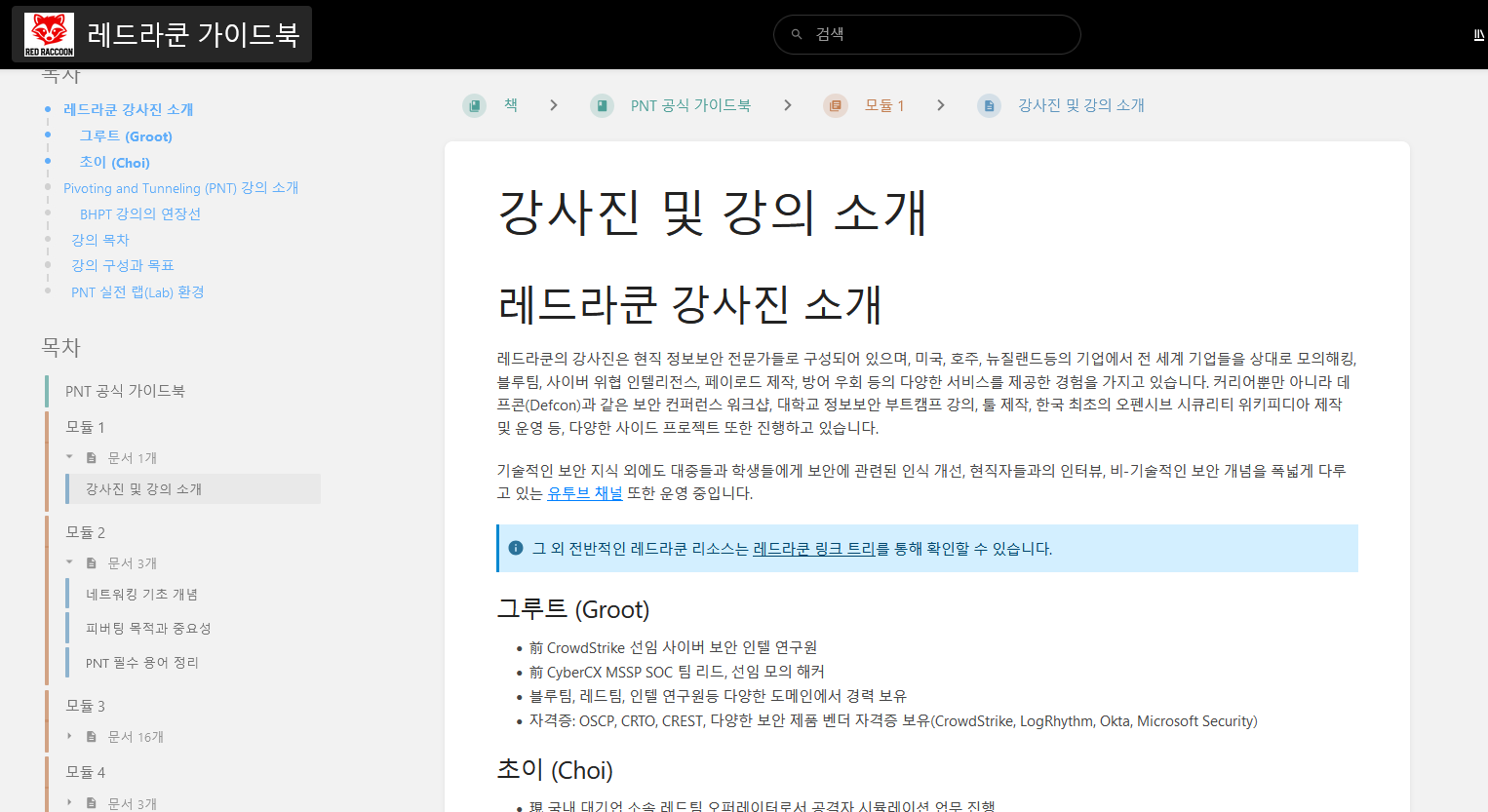
Red Raccoon Academy Instructors
Choi
Current Red Team Operator at a major domestic corporation - performing adversary simulation and penetration testing
Former Fortune 100 professional, performed internal, external, and web penetration testing for companies in the U.S. and worldwide
Created and conducted Blue Team and Red Team workshops at Defcon 30 and Defcon 31
Operating Korea's first offensive security open-source Wikipedia (RedTeam.com)
Global CPTC (Collegiate Penetration Testing Competition) 2020 - 1st Place, Team Leader
Certifications: OSCP, CRTO, CRTL, EvilGinx2 Phishing Mastery Course, Breaching the Cloud
Groot
Current Senior Cybersecurity Engineer & Cybersecurity Bootcamp Lead Instructor
Former CrowdStrike Senior Cybersecurity Intelligence Researcher
Former CyberCX MSSP SOC Team Lead, Senior Penetration Tester
Possesses career experience in various domains, including Blue Team, Red Team, and Intel Researcher.
Certifications: OSCP, CRTO, CREST, security product vendor certifications (CrowdStrike, LogRhythm, Okta, Microsoft Security, Netskope, etc.)















![[AWS Beginner's Guide] Master the Basic Network Configuration!Course Thumbnail](https://cdn.inflearn.com/public/files/courses/337818/cover/01jydvkvff56sgabnh2ekavg67?w=420)