Web Hacking & Secure Coding That Web Developers and Information Security Beginners Must Know
crehacktive
An introductory course on web hacking for information security beginners and web developers! Start web hacking in a fun way with this course!
Basic
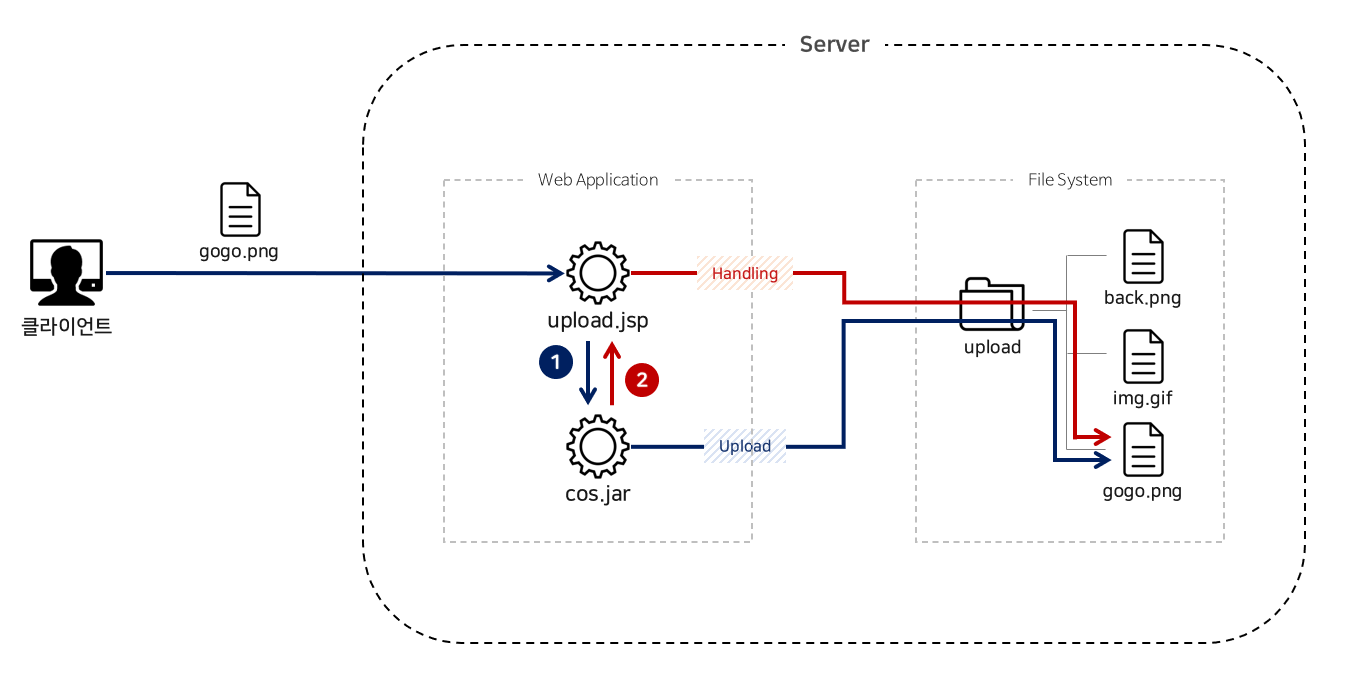
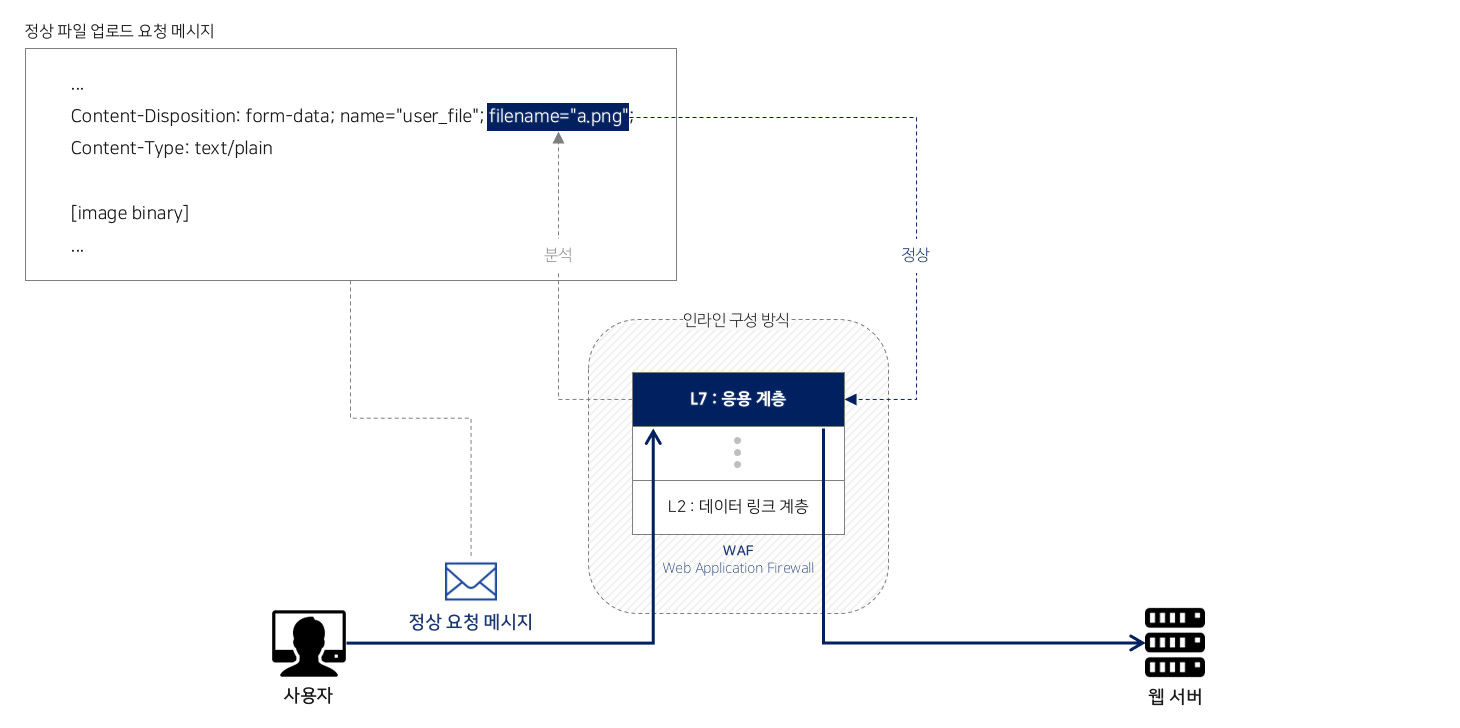
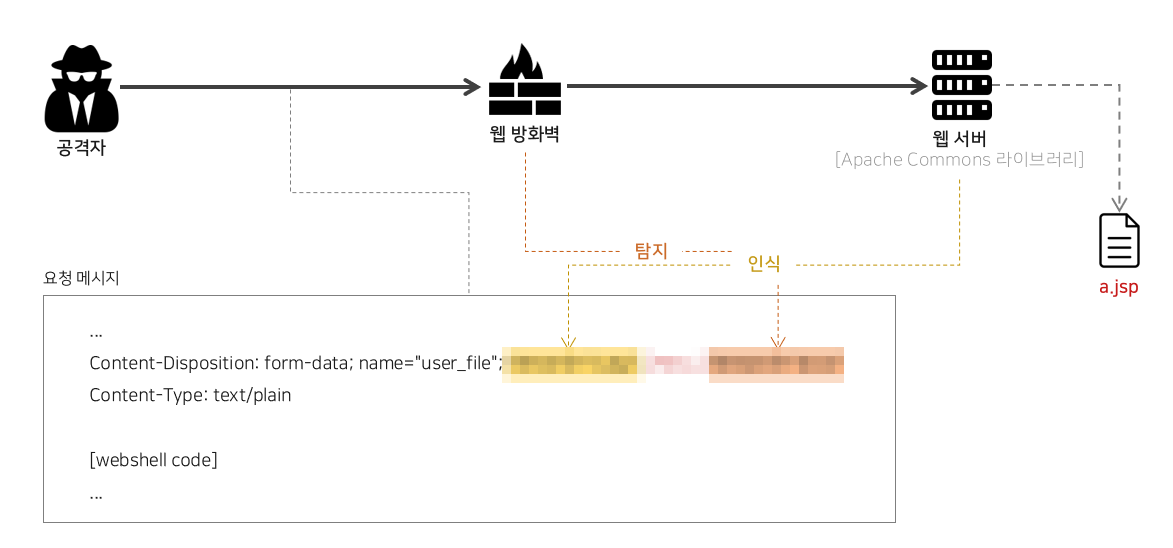
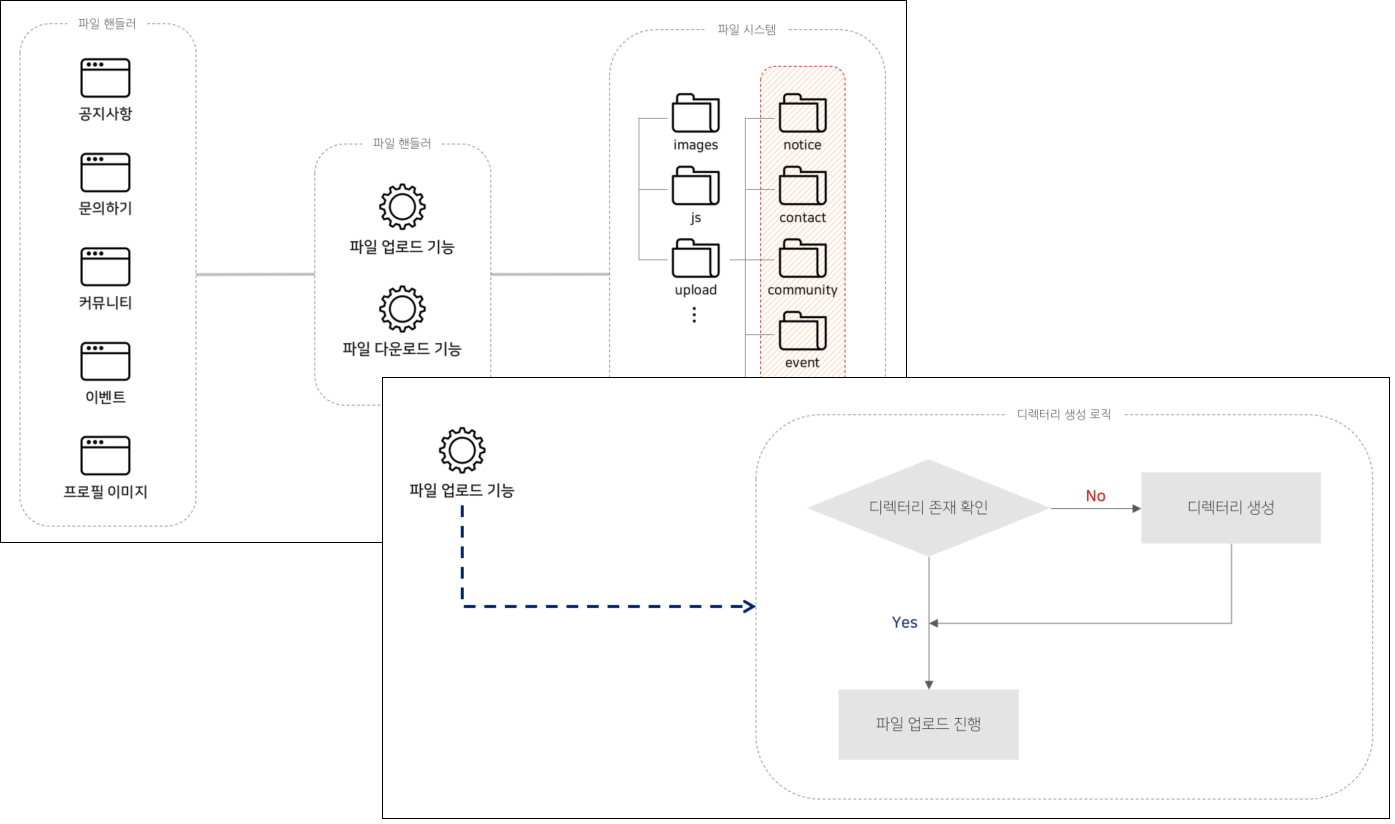
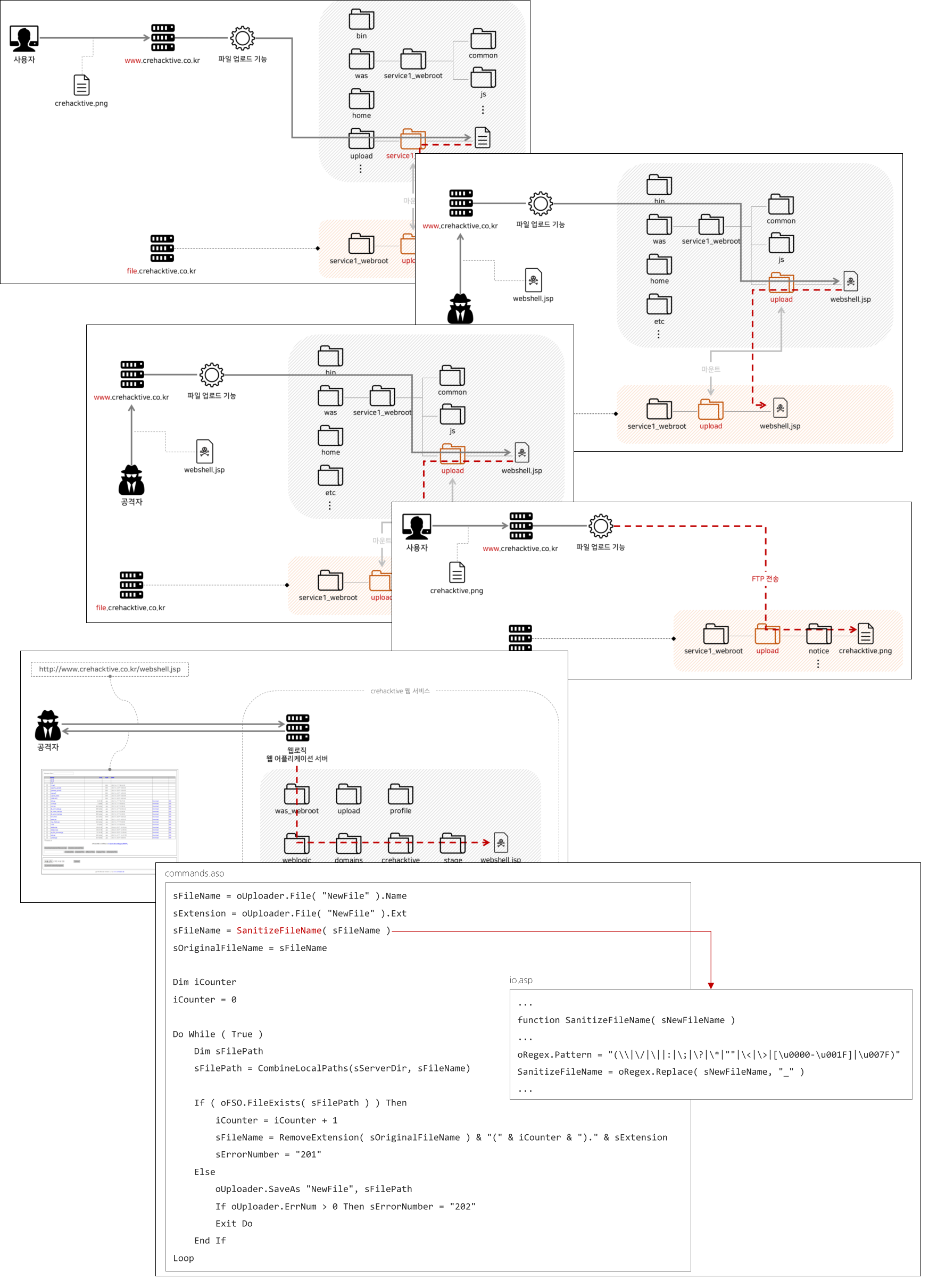
Penetration Testing, Injection