Basic SQL Grammar for Successful SQL Injection Attacks
crehacktive
The basic steps to learn SQL injection attacks, the flower of web hacking! This is a lecture on basic SQL grammar!
Basic
SQL, Penetration Testing, MySQL
An introductory course on web hacking for information security beginners and web developers! Start web hacking in a fun way with this course!
2,244 learners
Level Basic
Course period Unlimited

Reviews from Early Learners
5.0
진용훈
thank you
5.0
rlarudwn516
There was a lot of practical content during the lecture, so it was good to understand the attack principles and differences in each attack method that are difficult to understand through theory alone. I liked that the attack target, attack principles, and countermeasures (detailed code) for each vulnerability were systematically organized and explained well.
5.0
frenchkebab
I had to learn about security knowledge during a sudden job change, so I completed the course in 4 days. I really didn't know anything about security, but I was able to learn about where vulnerabilities can occur in the overall structure of the web. When I looked for lectures on the Internet, most of them seemed to only give an overview at a high level, but since there were examples, I remembered them a little more and was able to understand what kind of impact vulnerabilities have. However, I wish the setup guide for Mac users was a little more detailed. Other than that, I'm really satisfied with the lecture content.
Web Hacking and Security
Secure coding
Web hacking lessons for web developers and information security beginners!
Respond accurately to any risk situation, anytime.
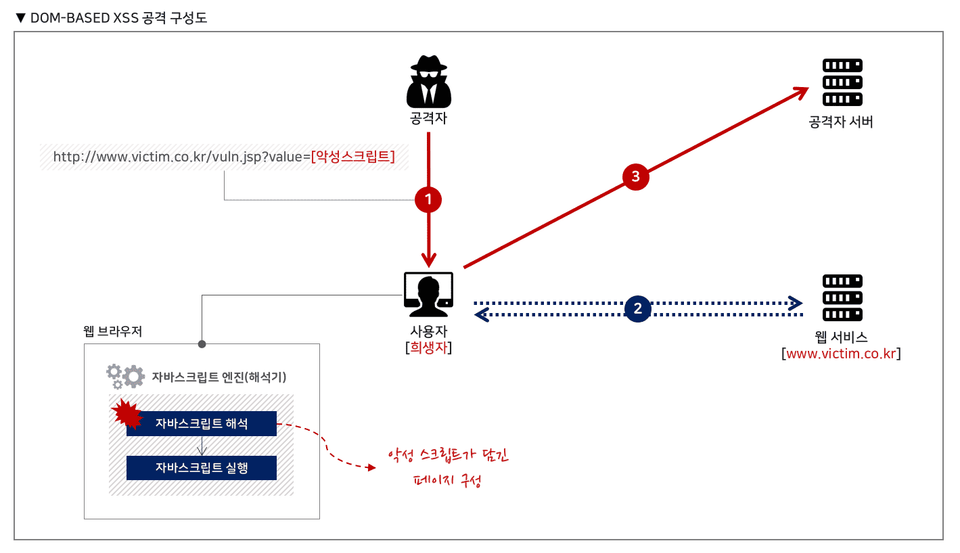
Knowing the attack will help you to see the defense! When you look at a web service from the attacker's perspective, you will see more vulnerabilities than when you look at a web service from the defender's perspective! Also, rather than simply knowing the countermeasure, you need to know the attack accurately to come up with the correct countermeasure for the situation!
Web services are being created, modified, and constantly adding features at this very moment. There are many cases where these features are created and web services are created without any knowledge of potential threats. In this situation , knowledge of web hacking is not optional but essential !
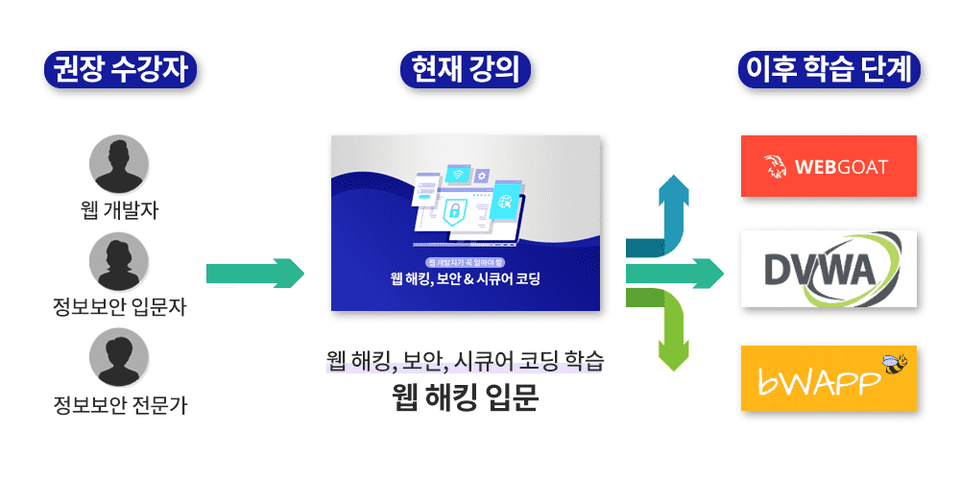
This is an introductory course on web hacking for web developers and information security beginners. Later, lectures will be opened on the famous vulnerable virtual environments , WebGoat / DVWA / bWAPP . Start your web hacking journey with this course!
(※ The vulnerable virtual environment of the course to be opened may change in the future.)
This is the main table of contents you will learn in this lecture.
There are a total of 9 web hacking attack items that you can learn through this lecture!
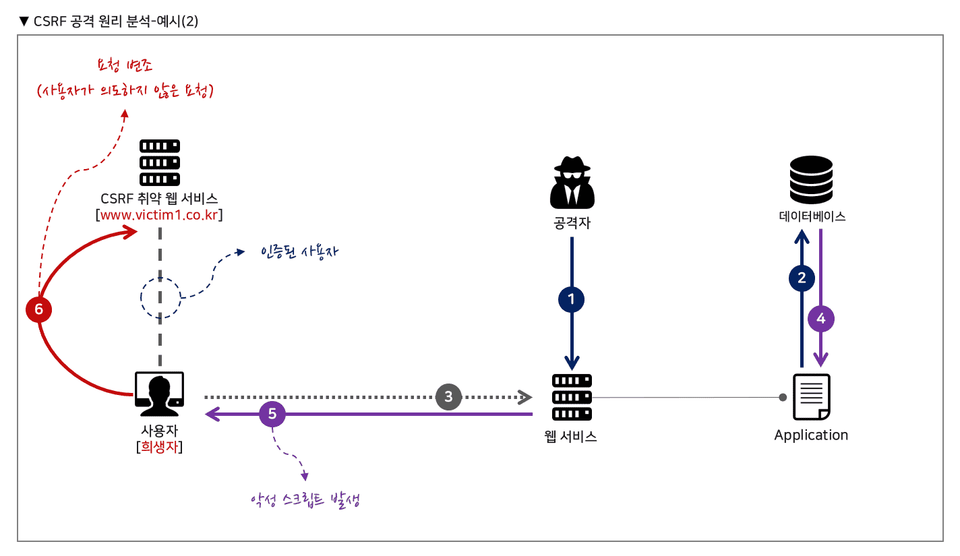
For each web hacking vulnerability item, you can learn more easily through detailed attack principle analysis, and you can identify the core of the attack, which is very important from both attack and defense perspectives.
We will conduct practical training that is easy to follow, and through a large amount of practical training, you will easily understand web hacking attacks, and through practical training that applies secure coding directly, you will practice defending yourself as well as attacking!
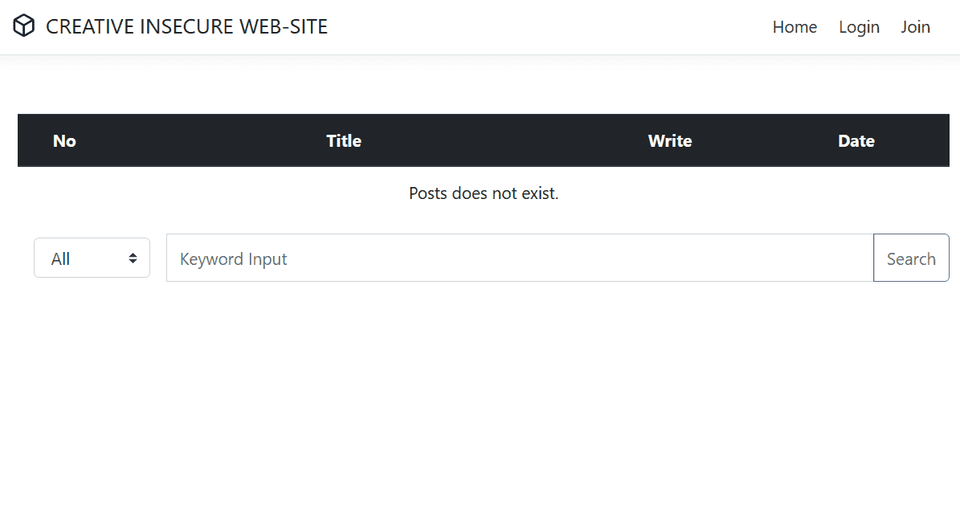
A vulnerable virtual environment website is provided for use during the training.
The unique features of Creative Education are the detailed principles of attacks, various attack practices, and secure coding practices. Many web hacking-related education programs end with attack practices, and only look at general countermeasures.
However! Creative's training will teach you everything from attacks to secure coding, and you will develop skills to respond to each environment!
Who is this course right for?
Information Security Beginner
Information Security Expert
Web developers who want to know about web hacking
Web developers who want to know about secure coding
Need to know before starting?
Web Basics
Web Programming
SQL Basic Grammar
27,340
Learners
1,519
Reviews
509
Answers
4.9
Rating
18
Courses
Hello, this is CreeHacktive.
Based on my years of experience diagnosing and researching various web services, I have been sharing practical, job-ready knowledge through the Inflearn platform.
I also authored Crehacktive's All-in-One Web Hacking Bible, which systematically covers the basics of web hacking. For those who lack foundational knowledge, I recommend starting your studies with this book.
Email : crehacktive3@naver.com
All
109 lectures ∙ (16hr 32min)
Course Materials:
All
252 reviews
4.8
252 reviews
Reviews 1
∙
Average Rating 5.0
Reviews 24
∙
Average Rating 4.9
Reviews 1
∙
Average Rating 5.0
5
There was a lot of practical content during the lecture, so it was good to understand the attack principles and differences in each attack method that are difficult to understand through theory alone. I liked that the attack target, attack principles, and countermeasures (detailed code) for each vulnerability were systematically organized and explained well.
Reviews 2
∙
Average Rating 5.0
5
It is clear that you have prepared the lectures with sincerity. Not only did I easily understand the major web vulnerability attacks, but I was also disappointed that many lectures only dealt with attacks, but you also provided information on secure coding and defense perspectives, so it was a meaningful lecture in many ways.
Thank you so much for recognizing the effort you put into the lecture! Everyone is only focused on offense, but defense is also very important~! Thank you so much for leaving a great review!
Reviews 5
∙
Average Rating 5.0
5
I had to learn about security knowledge during a sudden job change, so I completed the course in 4 days. I really didn't know anything about security, but I was able to learn about where vulnerabilities can occur in the overall structure of the web. When I looked for lectures on the Internet, most of them seemed to only give an overview at a high level, but since there were examples, I remembered them a little more and was able to understand what kind of impact vulnerabilities have. However, I wish the setup guide for Mac users was a little more detailed. Other than that, I'm really satisfied with the lecture content.
Check out other courses by the instructor!
Explore other courses in the same field!