プロのセキュリティアナリストの実務の華!
セキュリティアナリスト の基本スキル、情報通信網法第2条第1項第7号 によると、「侵害事故 」とは「ハッキング、コンピュータウイルス、論理爆弾、メール爆弾、サービス拒否、または高出力電磁波などの方法で情報通信網またはこれに関連する情報システムを攻撃する行為によって発生した事態」を意味します。" refers to "a situation caused by an act of attacking information and communications networks or related information systems through methods such as hacking, computer viruses, logic bombs, mail bombs, denial of service, or high-power electromagnetic waves."情報資産関連システムで発生する侵害事故は、システムおよびアプリケーションで異常動作が発生 したり、管理者が意図しない現象(削除、修正、流出など)が攻撃者によって発生 したりする場合を意味します。 サイバー侵害事故が発生した場合、企業は迅速に被害範囲を把握し、事故の収拾を通じてビジネスへの影響を最小限に抑えなければなりません。業界で求められる法規またはコンプライアンス遵守のために必要な活動が漏れた場合、関連法規や規定による処罰や追加の履行項目が発生する可能性があります。ビジネスへの影響を最小限にするため、企業のセキュリティチームや広報チーム、法務チームなど、全社的に事故対応に集中します。企業では、セキュリティ事故が発生した際に対応するために必要な必須活動を、模擬訓練を通じて年間または四半期ごとに実施しています。
セキュリティアナリストは、企業や組織で侵害事故が発生したり法的問題が生じたりした場合に、事故分析業務を遂行します。さまざまな原因で発生するシステム異常の原因を把握するためには、こうした問題状況を判別できる能力が必要です。特に、外部からの侵入や内部従業員による侵害事故が発生した場合、事故分析を通じてシステムの被害状況および侵害原因の分析業務を遂行することがセキュリティアナリストの役割です。
企業の事故被害を分析し、事故が再発しないよう対応策を導き出すためには、正確な事故原因を分析することが最も重要です。しかし、実際に事故分析の過程を経験することは非常に稀であり、難しいことでもあります。
「Big Root」 という用語は、一般的に問題や状況の複雑さを強調する際に使用されます。「Big Root」は問題の根源が大きく複雑であることを意味します。これは、問題が単純な原因や要因だけに限定されず、多様な要因が複雑に絡み合っていること を示しています。.
高度化されたサイバー攻撃による侵害事故も、表面化したシステム分析だけでは事故原因の問題解決が困難です。高度な攻撃によって事故が繰り返し再発し、企業のビジネスに持続的な被害を与えることになります。企業のセキュリティチームは、セキュリティ事故の根本原因(root cause)と侵入経路(vector)を特定するために、分析の過程で多様なシステムやソリューションの情報を確認する必要があります。
講義を通じて侵害事故対応の手順について説明し、企業に深刻な被害をもたらすサイバーセキュリティ事故の類型と原因について学習します。ハッキング事故の原因となるセキュリティ脆弱性を根本的に解決するために必要な能力を学習します。
概念から実務まで 実務事例に類似した侵害事故分析トレーニングを通じて、
セキュリティアナリストとしての業務を遂行するための基礎知識を身につけ、分析ツールを実習します。 ネットワーク通信とアプリケーションへの理解に基づき、サイバーセキュリティ事故の原因を突き止めます。 様々なセキュリティ機器から発生する脅威ログを分析し、侵入を試みる攻撃者を特定することができます。 企業への侵入対応および分析業務の遂行に必要な、実務的観点からの侵害事故分析手法を学習します。 この講義では、企業における侵入対応および分析業務の遂行に必要な、実務的観点からのインシデント分析手法 を共に見ていきます。ネットワークベースの侵入検知ログやネットワークパケット分析業務を行う実務担当者に、セキュリティアナリストが分析時に必要とする知識や分析ツールの活用ノウハウを提供し、分析を通じてどのような結果を見つけ出すべきかを説明します。
特に、セキュリティ分析業務を遂行していると、多様なログや分析ツールを使用することになります。侵入検知システム(IDS)のログ分析、Webサーバーログ、ネットワークパケット分析業務に携わりたい方のために、脅威分析の基礎概念と実務技術を説明しようと思います。基本概念および技術と、著者が業務で習得したノウハウも併せて説明することで、受講生の皆様の業務遂行能力を向上させる一助となれば幸いです。
事故分析のために分析する情報は、代表的なものとしてウェブログ、IDS/IPSログ、ネットワークパケットログがあります。実際のセキュリティ事故が発生したシステムのログを分析しながら、事故対応訓練を実施 する予定です。最後に、キャリア管理の観点から、今後どのようにキャリアを築いていくかについても共有する予定です。
効率的な分析学習 を
侵入対応/分析
侵害対応/分析
侵害対応/分析
1) 侵害対応/分析の実務者が使用する分析ツールおよび手法の技術を学習します。 侵害事故の分析経験が少ない場合、事故調査の際にどこから分析を始めるべきか途方に暮れることがあります。本講義では、分析者が迅速に事故原因を特定し、攻撃経路を識別できるよう、タイプ別の事故事例を実習します。実習を通じて、セキュリティログを分析する際に侵害事故の痕跡を見つけるために何に集中し、どのようにすれば効率的に分析できるかを学ぶことができます。
✅ 正常ログの判別基準の事例学習 ✅ 大量ログ分析プログラムの使用実習 ✅ 侵害事故タイプの学習 2) ハッキング手法に依存しない分析方法を通じて、多様な状況への適用および応用が可能です。 攻撃者たちはさまざまな方法でシステムへの侵入を試みます。特定の攻撃ツールや攻撃手法に依存せず、脆弱性を悪用する原理を理解することで、多様なセキュリティ攻撃の試みに対して応用し、分析を行うことができるようになります。
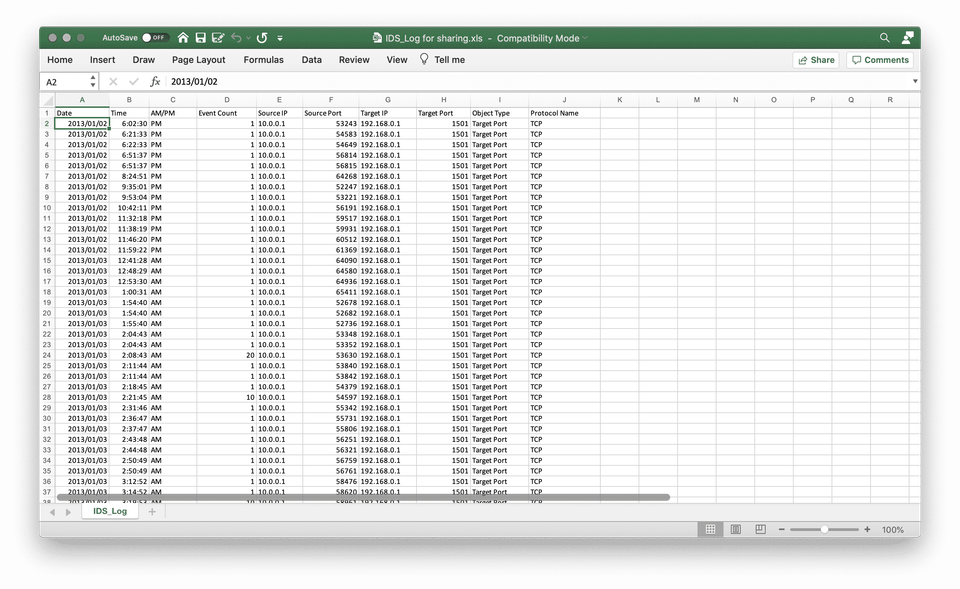
訓練のためのセキュリティ分析実習 。 IDSログ分析訓練 商用セキュリティ製品で検知された攻撃行為ログの一部をフィルタリングし、実習用に提供します。攻撃イベント名、攻撃時間、その他の情報は、実際の事故事例と同様に構成されています。
Webログ分析訓練 Webサーバーを対象に行われた攻撃手法と、攻撃対象のサーバーに残されたログを直接分析します。分析を通じてWebサーバーの脆弱な設定を把握し、事故の原因を特定します。
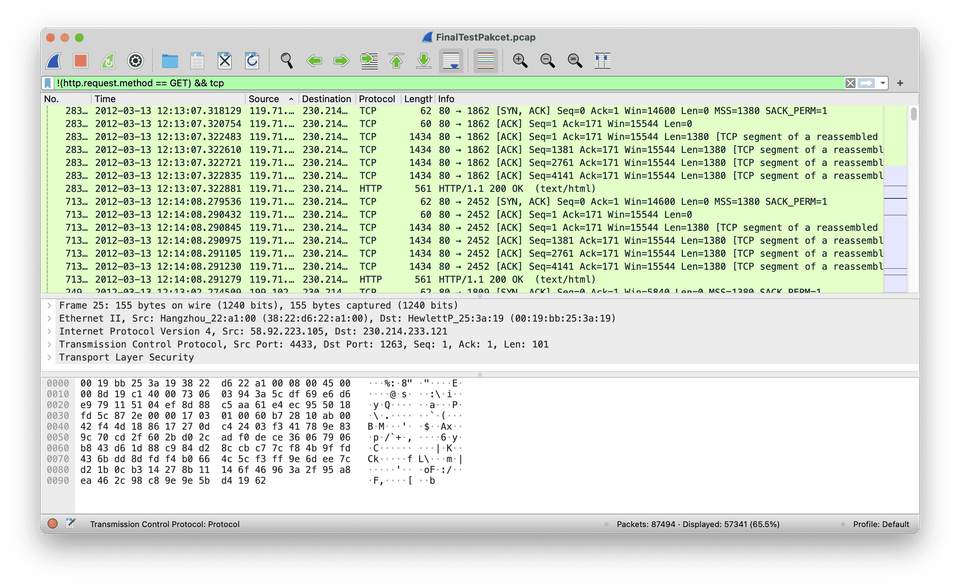
ネットワークパケット分析 サイバーセキュリティ事故の事例をラボ環境で同一の条件で再現し、攻撃者の視点からシステムを攻撃する過程を再現してネットワークトラフィックをキャプチャします。キャプチャしたパケットを分析し、攻撃対象と被害範囲を分析します。
実習に使用されるログの攻撃者IPおよび攻撃対象IPは、実習のために修正されています。 学習内容 📚 それぞれの実習事例を通じて侵害事故分析を実習し、分析プロセスを学習することができます。分析プロセスを通じて学習する前に、まずは自身で分析を行ってみた後、自ら分析した過程と分析ガイドの内容を比較してみます。
セクション 1 - 事前学習 実習に先立ち、分析に必要な手法について確認します。特定のパターンに基づいて攻撃行為を識別する方法と、振る舞いに基づいて閾値を設定し脅威を識別する方法に分けて分析する手法を学習した後、映画の中の異常行為識別の事例を通じて、セキュリティ事故の事例に適用する方法を一緒に見ていきます。
映画の中の異常行為識別事例の参考動画 (クリック)
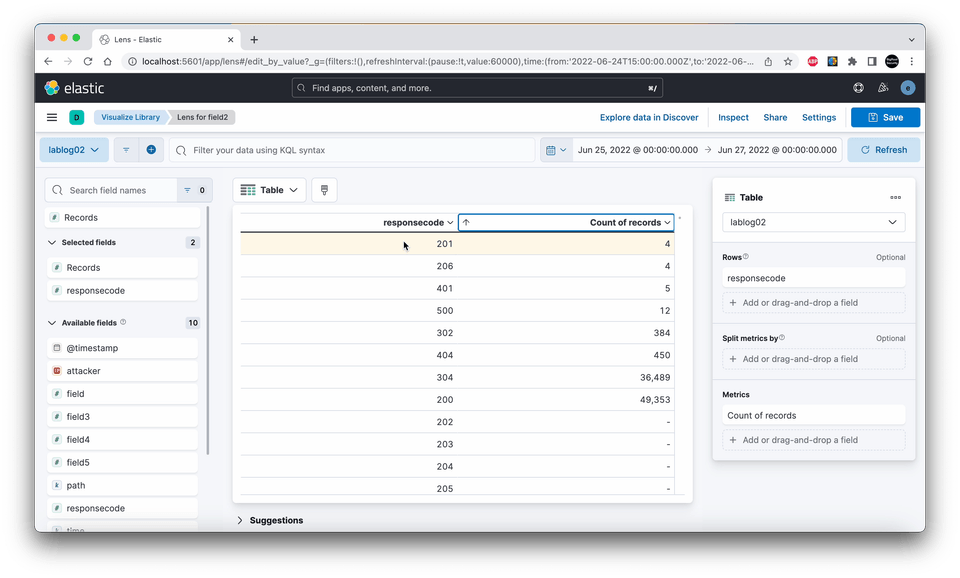
セクション 2 - 侵害事故対応分析実習 1:IDSイベント分析 特定期間中に検知された侵入検知ソリューションのイベントを分析し、大規模なネットワーク障害を引き起こした原因を分析します。次の表は、侵入検知システムから抽出した侵入検知イベントです。
検知項目
検知情報
イベント収集期間
3 ヶ月
検知シグネチャ名
TCP_Invalid_SACK
送信元 IP
10.0.0.1
送信元ポート
ランダム
宛先 IP
ランダム
宛先ポート
ランダム
合計
1441 件
TCP_Invalid_SACKという侵入検知システム(IDS)のシグネチャは、非正常なSYNパケットとACKパケットによって発生します。一般的にTCP通信は、プロトコルで定められた方法で必要な通信パケットをやり取りします。しかし、通信に使用されるプログラムやネットワークの特性によって、定められたプロトコルとは異なる方式で通信する現象が発生します。TCP_Invalid_SACKシグネチャは、このような現象を記録します。
このような理由から、攻撃者が非標準的なプログラムを使用する場合でも、通信内容が検知されます。もちろん、検知された情報には攻撃者の通信だけが記録されるわけではありません。検知された1441件のイベントのうち、攻撃者が通信した回数は少数でしょう。セキュリティアナリストは、イベント分析を通じて少数の攻撃検知事例を見つけ出す必要があります。
実習ログファイルを用いて直接分析する過程を通じて、事故の原因を追跡します。事故原因に関する分析結果は、分析ガイドセクションで説明します。以前にも強調しましたが、事故分析の過程をまずは自身で直接分析し、分析ガイドセクションの内容を参考にしながら、自ら分析した内容と比較することで事故分析のトレーニングを行います。
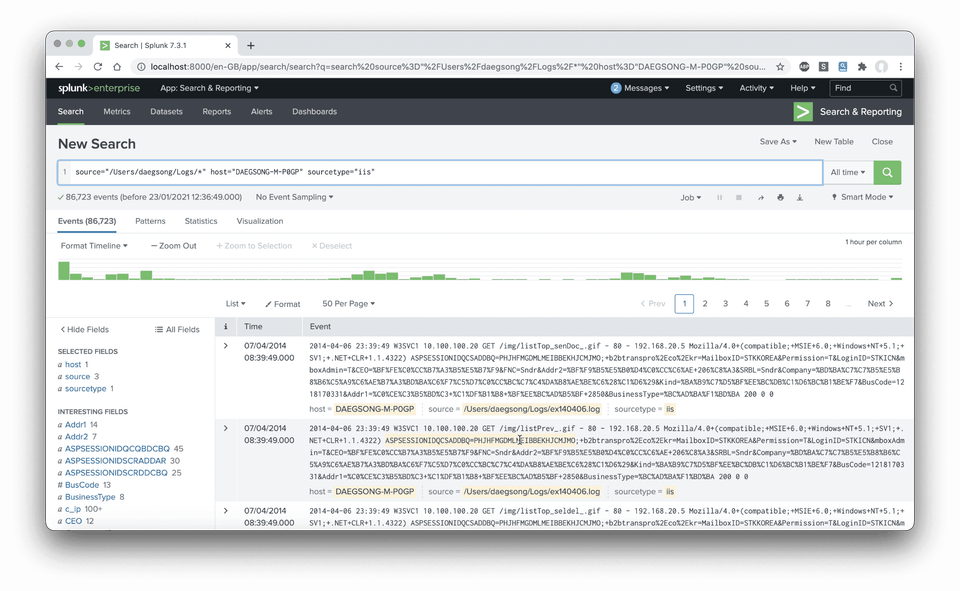
セクション 3 - 侵害事故対応分析実習 2:アプリケーションログ分析 ウェブログ分析を通じて、侵害事故が発生したシステムの事故経緯を分析します。ログの加工作業は、分析されていない情報や不要な情報を整理し、より効率的にイベントを分析するための作業です。しかし、このようなトラフィックは干し草の山のように膨大です。干し草の山に隠れている針のような攻撃トラフィックを見つけ出すことは、決して容易なことではありません。
2番目の実習では、ウェブログを利用して藁の山を片付ける方法を一緒に見ていきます。Splunk、Log Parser、Elasticsearchをインストールし、Windowsウェブサーバーのログ分析プロセスを実習してみましょう。
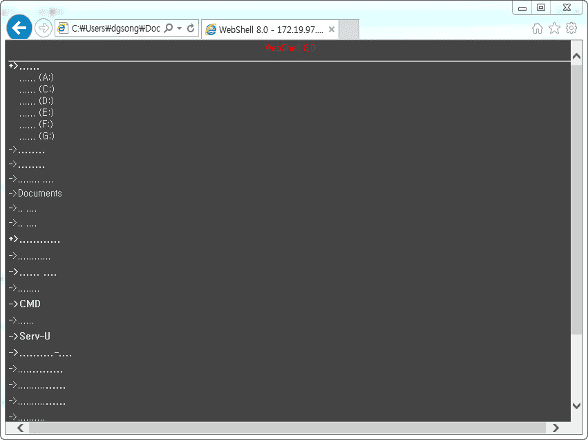
セクション 4 - 侵害事故対応分析実習 3:ネットワークパケット分析 ファイル拡張子の制限を回避した攻撃者は、掲示板にアプリケーション実行ファイル(ASP拡張ファイル)をアップロードし、システムを掌握します。ネットワーク通信を通じて行われたウェブシェル攻撃を分析してみましょう。パケット分析の過程において、分析対象となる通信やサーバーの分析範囲を選定する作業だけでも、侵害分析を非常に効率的に遂行できるようになります。ウェブシェルの通信パケットを分析するために、分析時に使用するフィルタ構文を活用して、効率的にパケットを分析していきます。
分析の過程で、実際のネットワーク通信を通じて実行されたバックドアファイルを抽出してみて、どのような通信が行われ、サーバーにどのような被害を与えたのかを再現を通じて追跡してみましょう。
Q&A 💬 Q. 学習するために必要な予備知識は何ですか?
本講義は実習中心に構成されています。サイバーセキュリティに関する基本的な概念や理論は含まれていません。本講義の実習を遂行するためには、IDSについて理解しており、ウェブアプリケーションの設定とウェブサーバーのレスポンスコードについての理解が必要です。予備知識は必要ですが、ハッキングの経験がなくても侵害事故分析を行うことができます。
Q. 他のセキュリティ講義と何が違うのですか?
セキュリティ事故分析の手法やノウハウに関する実務経験を中心に、講義コンテンツを構成しました。3つの侵害事故分析事例はすべて実際の事故事例を脚色しているため、セキュリティ事故分析の経験値を高めることができます。ただし、ディスクイメージを収集する法的意味でのフォレンジック工程については扱いません。
Q. 受講に関する注意事項はありますか?
実習は公開ツール(MS Log Parser Studio、Wireshark)とフリートライアルのセキュリティ製品、Microsoft EXCELを使用します。実習内容には分析製品をインストールする過程は省略されています。各製品ごとのメーカーのインストール案内リンクを参考に、受講生が個別にインストールを行う必要があります。
この講義の知識共有者は ✒️ ビッグルートセキュリティ CERTチームの侵害事故対応専門家および外資系セキュリティ企業のソリューションエンジニアとして18年目活動しています。韓国IBMでSOC構築プロジェクトと運営プロジェクトのPMを担当しました。セキュリティインフラの設計と構築・運営プロセスの開発業務を遂行しました。アンラボ(AhnLab)のCERTチームで、民間企業や公共機関のセキュリティ侵害事故の分析&対応業務を遂行しました。3.20 DarkSeoul(ダークソウル)キャンペーン発生当時、国内放送局のシステム点検を遂行し、Nate個人情報流出事件の際には、事故流出システムに対する点検を支援しました。
主な経歴
セキュリティコンサルタント:セキュリティインフラコンサルティングを通じたセキュリティ強化戦略の設計/構築/運用 セキュリティ管制コンサルティング:SOC構築コンサルティングおよび運営業務の遂行 セキュリティサービス商品開発:次世代セキュリティ監視ソリューション&サービス開発 侵害事故対応:軍/公共/民間企業など多数 2014 KISA K-Shield セキュリティ修了講師 (AhnLab ネットワークフォレンジック教育担当講師) 2016 個人情報保護 PIS(Personal Information Security) FAIR / 発表テーマ ‘Security Intelligence’ 사이버 침해사고 분석 전략 (에이콘출판사, 2016) 저 해킹, 침해사고분석 (지앤선, 2009: