![[Eduwill White Hacker Training Course] Malware CreationCourse Thumbnail](https://cdn.inflearn.com/public/courses/329633/cover/9a4806ae-b981-4509-9209-923b1e405631/329633-eng.png?w=420)
[Eduwill White Hacker Training Course] Malware Creation
eduwill
Let's create malware such as ransomware and Trojan horses ourselves, and learn how to bypass antivirus software!
Intermediate
Malware
APT malware production technology is the process of producing the fundamental code process of vaccine bypass and information security breach attack technology by producing advanced (upper) malware rather than basic malware production. Don't miss APT, the essential element of hacking!
Creating malware in C language
Understanding how the program works
Process Hollowing Implementation
Implementing system calls directly
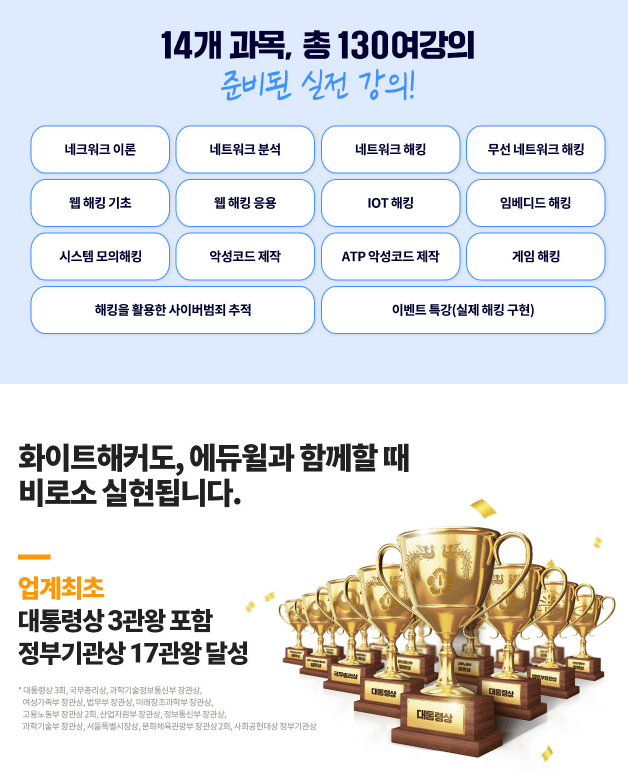
Eduwill's white hat hacker training course!
📢 Please check before taking the class!
Introducing the subjects of the 'White Hacker' course :)
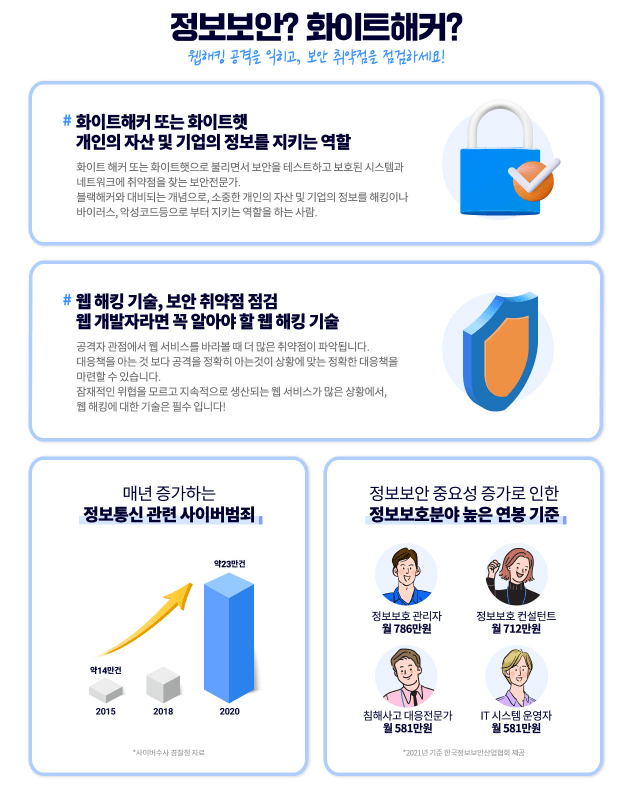
APT (Advanced Persistent Threat)
This refers to an attack that involves continuous hacking attempts against individuals, government agencies, or companies to leak personal information or important data.
To put it more simply, hackers set a specific target, approach it with a plan, watch for a certain period of time, and then leak all data when security is vulnerable.
Recently, the number of files that can be infiltrated from outside sources, including through email, USB drives, smartphones, and network data transmission systems, and the number of cases of damage are increasing. We must not overlook the fact that even our country can be compromised by hackers, stealing national infrastructure, personal information, and confidential information using a single USB drive. Furthermore, malware and APT attacks can infect individuals not only by executing executable files infiltrated from outside sources, but also by simply opening documents containing malware. Ransomware is a prime example.
As such, malware and APT attacks are becoming increasingly sophisticated and sophisticated. They are becoming targets not only for individuals, organizations, and businesses, but also for nations, making effective blocking and management crucial. This course will teach you how to create APT malware and how it is used in hacking attacks through hands-on practice.
Knowing how to attack will help you develop the ability to find vulnerabilities and respond/block them!
📢 Please check the precautions!
Q. Can non-majors follow along?
Yes, of course you can. However, there are some prerequisite knowledge required for learning, so be sure to check the [Prerequisite Knowledge] section below!
Who is this course right for?
People working at information security companies
A student majoring in Information Security
Anyone who wants to learn hacking
Need to know before starting?
This is an advanced (high-level) malware hacking course, and you must have knowledge of hacking and malware creation methods at a beginner or higher level.
All
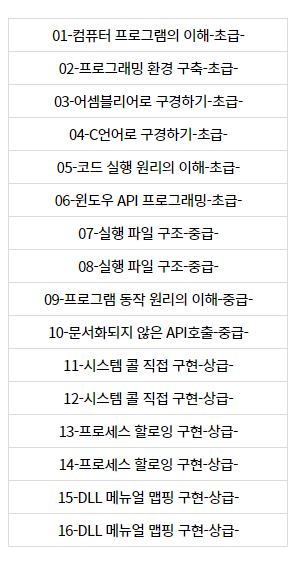
18 lectures ∙ (14hr 53min)
Course Materials:
All
9 reviews
4.6
9 reviews
Reviews 1
∙
Average Rating 5.0
Reviews 5
∙
Average Rating 4.8
Reviews 7
∙
Average Rating 5.0
Reviews 1
∙
Average Rating 5.0
Reviews 2
∙
Average Rating 4.5
Check out other courses by the instructor!
Explore other courses in the same field!
$136.40