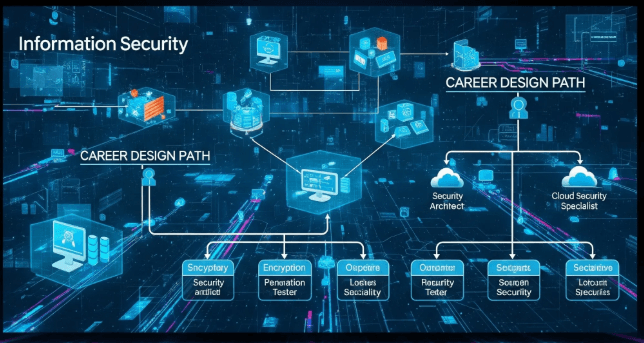
(SEC_Step_03) Hacking Techniques Explained by the Byte Detective: From Security Threats in the Cloud Era and Beyond
88888
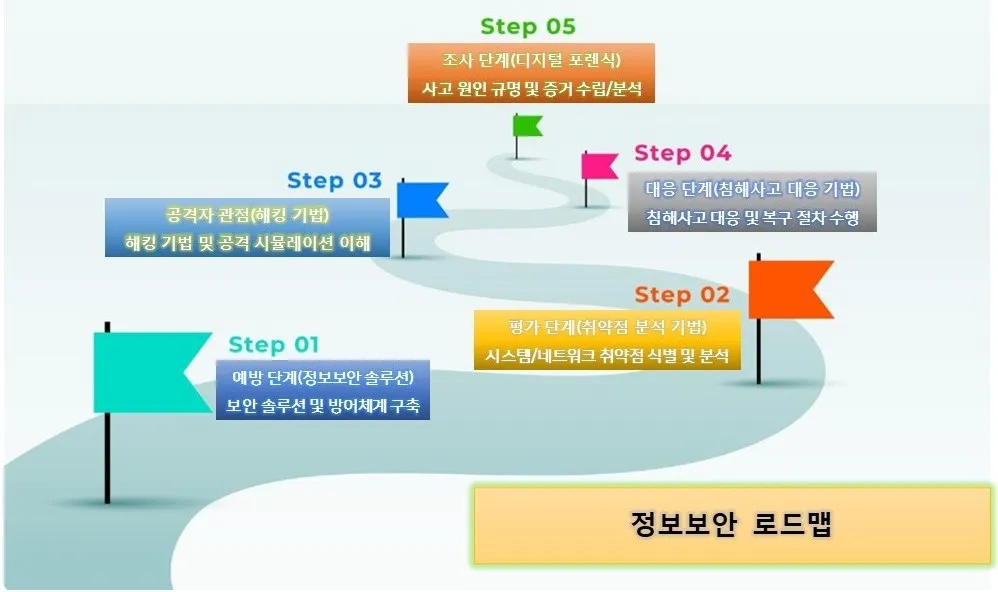
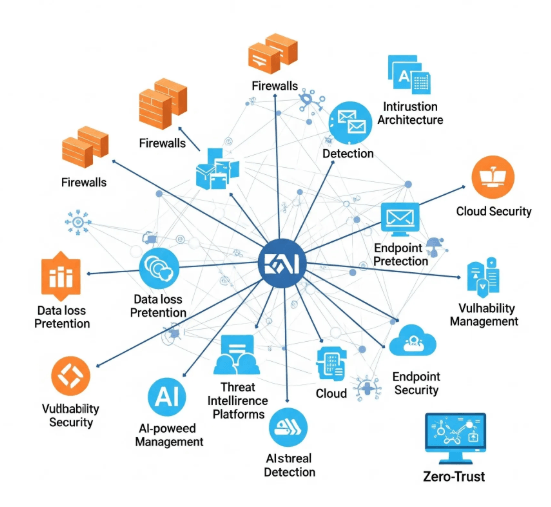
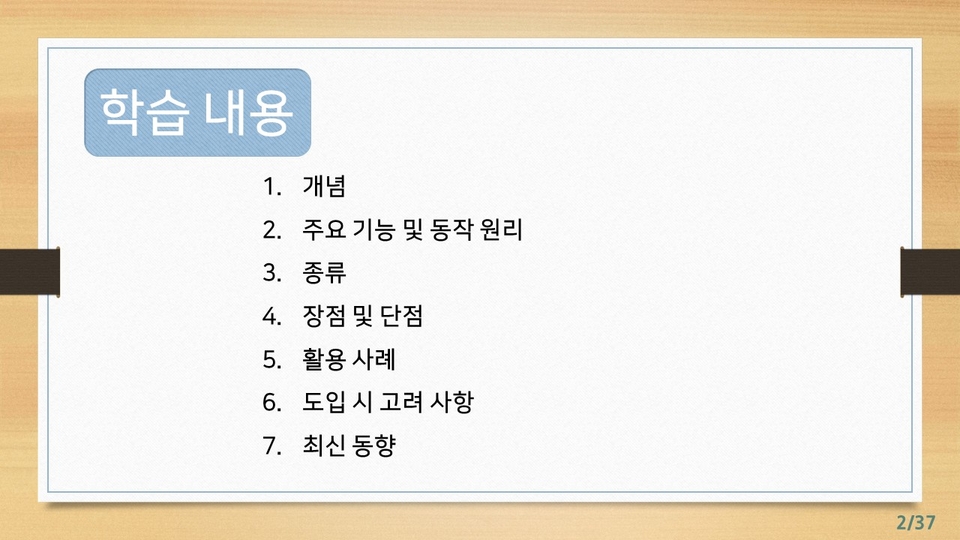
This is an introductory information security course that breaks down complex cyberattack techniques as easily and engagingly as a movie. From traditional hacking methods to attack techniques occurring in the latest cloud environments, everything is organized for easy understanding based on real-world cases and scenarios. Even if you don't know technical terms, anyone can follow along through the active use of analogies, visual aids, and storytelling, structured so that vague security concepts remain clearly in your mind. "This course is designed for those who only had a vague knowledge of security to understand everything at once—from the principles and flow of hacking to actual attack methods and response strategies."
Beginner
Penetration Testing, System Hacking, Hardware Hacking














![[D-PEC UP_PASS] National Certified Intellectual Property Ability Test (IPAT) Preparation (Core Compression)Course Thumbnail](https://cdn.inflearn.com/public/files/courses/338414/cover/ai/2/7df16b1f-6503-44f6-90c2-3a4b00802b72.png?w=420)
![[D-PEC UP_PASS] National Certified Service Management Ability Test (SMAT) Module A_Business CommunicationCourse Thumbnail](https://cdn.inflearn.com/public/files/courses/334735/cover/ai/3/057c9d51-2f2d-4c4a-853a-733e8b5ad4f2.png?w=420)




![[D-PEC UP_PASS] Test of Information Security (TOLIS)Course Thumbnail](https://cdn.inflearn.com/public/files/courses/335790/cover/01k1fkg3ge5sb67f0xdtesh791?w=420)

![[D-PEC UP_PASS] Nationally Certified Industrial Security Expert (ISE)Course Thumbnail](https://cdn.inflearn.com/public/files/courses/333129/cover/ai/0/67228f11-355f-4e72-86c5-4c7d1b906a63.png?w=420)